A guide to Identity Theft
“Open up – everything’s waiting for you”..
A few weeks ago, while enjoying a pint at one of Halifax’s finest watering holes, I came across a poster pinned to the wall, advertising the date and time of an upcoming Fleetwood Mac “tribute” band.
I’m sure they’re very good, but ironically, the band is called “Go your own way”.
There may be some original material in the set, however, it’s more likely they will be going the way of the 5-piece superstar band known all over the world instead.
They’re only one of countless Elton Ron’s, No-Asis, and Amy Housewine’s treading the boards all across the country and it seems that people lap this stuff up.
Legally speaking, any act can cover a song during a live performance as a result of licenses obtained and paid for by venue owners to performance rights organisations (PROs).
To provide context, PROs represent songwriter, composer and music publisher members’ performing rights, and collect royalties on their behalf when their music is played, or these acts perform publicly.
Frankly, they’re fooling nobody, and they aren’t even trying to, “it’s a tribute”. Although they do mimic loads of body movement, drawly type of delivery, cod mannerisms and all nature of wardrobe malfunctions which have been perpetrated by the original act down the years, which frankly make it seem like more of an impersonation than a tribute, anyway I digress.
There have been plenty of legal challenges through the years, however, the original artists largely seem to let it go and stand aside whilst Motorheadache and their ilk, do their worst, I’d imagine Lemmy laughing in his grave though TBF.
Conversely, the Infosec community is entirely preoccupied, and rightly so, with protecting individual user identities and Corporate IP from those who seek to misuse them for their own gain, by “pretending to be someone they are not”.
It’s less of a “tribute” and more of an actual crime, as laid down by the computer misuse act.
What’s even more troubling, is the resale of any harvested identities on the dark web. Password reuse is rife and people who don’t use password management tools regularly re-use the same password and user combinations. Even allowing for minor changes, it still reads like a greatest hits list, with the same dozen or so combinations on a continuous loop.
Allow for missing Multi-Factor Authentication (MFA) and you have the equivalent of an open-house policy for any public-facing resources.
Our ethical hacking teams have some of the brightest minds, and tricksy-testing-sneaky-super-clever-good stuff up their sleeves, but honestly, we can often unlock many systems with a 90-second visit to our dark web monitoring platform.
So if you think it’s odd that Brenda from accounts logged on at 3:45 AM, you’re probably right, it was more likely Sergei, or BR£NDA as he likes to call himself. By the way, if you ask him, he’ll probably say he does a mean Lancashire hotpot, and he’s been happily married to Stanley for twenty-five years.
All of a sudden BR£NDA doesn’t seem like such a funny play on words as a stage name, does it?
After all, that’s your company’s £ that he’s using, in the middle of his handle.
We aren’t bashing Brenda here, if your policy is to allow rotation or incrementation of passwords, then you’re at least culpable. If you don’t have a complex password policy or insist that your users have a unique corporate password, you’re partly to blame.
We’re not advocating full-on password-less access (unless you really want to – and it’s coming anyway) but let’s not make it easy for BR£NDA to impersonate the original user.
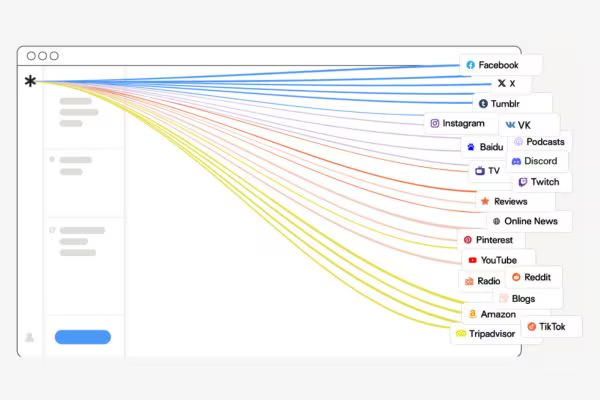
Consider some kind of dark web monitoring service, like the one we provide (Check out page 18 of the service catalogue, here when you’ve finished reading)
We often bundle this into our customer’s agreements, it’s been proven to have worked on many occasions and frankly, it’s so cost-effective, that you’d be mad not to.
It will show you which of your corporate credentials are for sale on the dark web immediately, and then alert you to new password leaks, allowing you to quickly check that your organisation isn’t at risk from “tribute acts” masquerading as your loyal staff.
Your data and your company secrets are your IP, there is nobody compensating you in the event that your IP is reused or resold and years’ worth of corporate advantage can be overturned in an instant.
People are entertained by “harmless” tribute acts all over the world, but there’s no fun in the reputational and financial damage that can be caused by allowing a threat actor into your systems.
Get in touch. Ensure details of a company breach are just unfounded “Rumors”
Sorry about that last one.