Introducing
next-gen vulnerability management: SmartScan
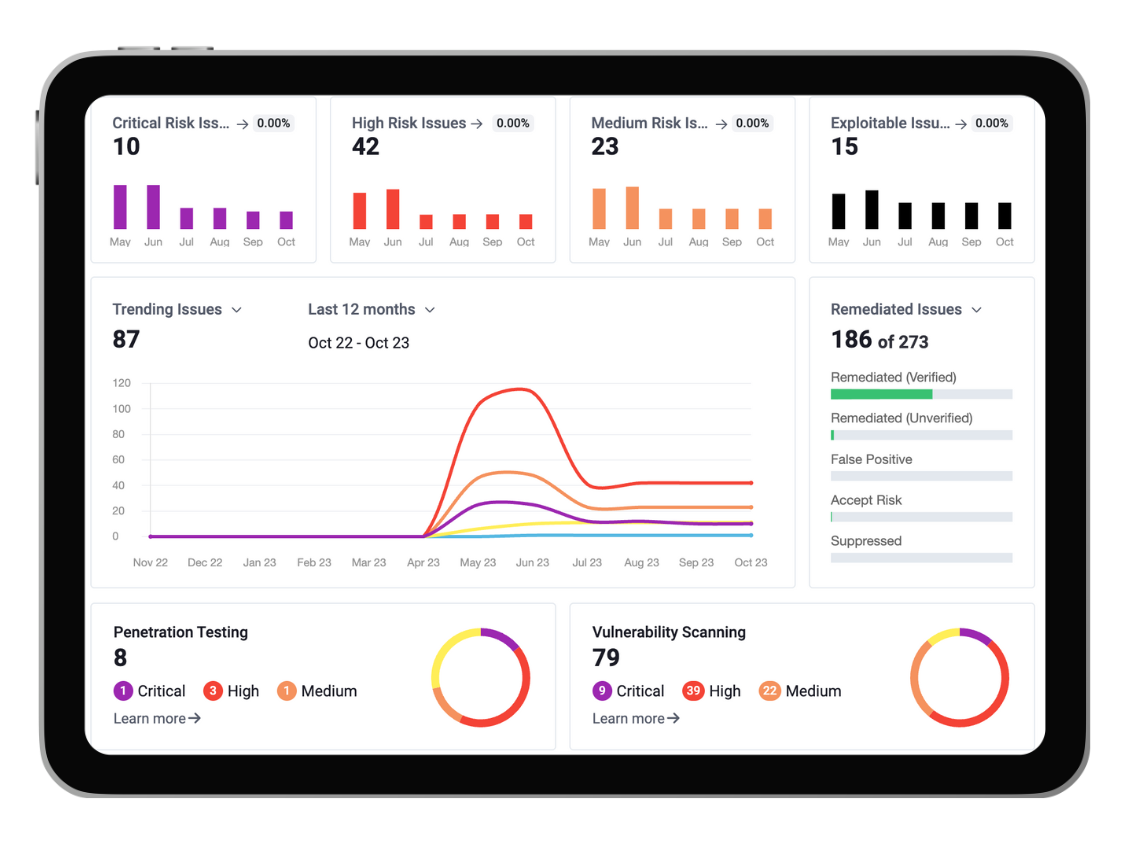
Our SmartScan service is designed to make your vulnerability management easier and save you time, by giving you full visibility over your IT estate, presenting your vulnerabilities in one pane of glass.

Malina Henea
7th March 2024
The importance of cyber security for organisations of any size is more pronounced than ever now as the digital domain expands and evolves. Cyber threats are not only increasing in sophistication but also in frequency, highlighting a crucial need for effective vulnerability management and detection mechanisms.
Cognisys’ vulnerability management service, SmartScan, is aimed at pinpointing and managing security vulnerabilities through state-of-the-art scanning technologies. It provides organisations with an in-depth view of their security weaknesses, empowering them to proactively enhance their defences against cyber threats. SmartScan is a service at the forefront of identifying, evaluating, and assisting in mitigating digital vulnerabilities. Some key elements of the service are its functionality, benefits, range of ingestion tools, and how it operates, underlining its role as an essential asset in maintaining cyber security measures.
Features of our vulnerability management service
Automated scanning
SmartScan streamlines the vulnerability detection process, minimising the need for manual intervention. It keeps constant vigilance for new threats, ensuring systems are always evaluated against the latest cyber threat intelligence (CTI).
Dynamic remediation
SmartScan automates the process of marking resolved issues as remediated by comparing new and previous scan results to identify fixed vulnerabilities. This feature streamlines vulnerability management, especially in large digital estates, and accelerates remediation verification, offering users control over which issues to officially remediate.
In-depth reporting
SmartScan produces thorough reports post-scan, detailing discovered vulnerabilities, their criticality, and suggested corrective actions. These insights are critical for grasping your security posture and prioritising improvements.
Up-to-the-minute threat intelligence
The portal is powered by Velma AI, a cyber security solution that leverages current threat intelligence to proactively identify emerging vulnerabilities and threats, keeping organisations ahead in protecting their assets. With continuous scanning of user environments, thousands of information sources are analysed to detect any actively exploited issues by threat actors, promptly alerting users for immediate action.
Service level agreements
SmartScan supports remediation management by enabling SLAs to track and benchmark remediation efforts. It offers notifications for SLA breaches, insights into remediation times, and tools for prioritising critical issues, thereby optimising the process and reducing the time to remediate.
Tailored scanning
SmartScan’s flexible scanning options allow for customisation to meet unique organisational needs, whether it is targeting specific areas or scheduling scans for minimal disruption.
Seamless integration
Designed to integrate with a multitude of tools and platforms such as exploit intelligence, scanners, ticketing systems, single-sign on and penetration testing tools, SmartScan enhances vulnerability management efficiency without disrupting existing security workflows.
Benefits of our vulnerability management service
Improved Security Framework
SmartScan’s proactive identification of vulnerabilities significantly lowers the likelihood of cyberattacks, fortifying your security framework.
Cost efficiency
By pre-emptively managing vulnerabilities, SmartScan helps in preventing the financial and reputational damage stemming from data breaches, offering a cost-efficient alternative to post-incident recovery.
Compliance requirements
SmartScan aids in achieving and maintaining compliance with certifications such as Cyber Essentials Plus, PCI, HIPAA, GLBA, ISO 27001, NIST by ensuring effective security controls and timely vulnerability remediation.
Efficiency and time savings
The automation and integration features of SmartScan free up IT and security teams to concentrate on broader strategic issues.
How our vulnerability management service works
Setup and configuration
Initially, SmartScan is tailored to your organisation’s environment, setting the scope for scans and integrating with other toolsets.
Automated scans
According to the agreed upon schedule, SmartScan runs automated, and provides comprehensive evaluations of your infrastructure.
Analysis and reporting
Each scan results are analysed, with a detailed report to outline vulnerabilities, their severity, and remediation advice.
Remediation and verification
Based on SmartScan’s findings, when vulnerabilities are addressed, subsequent scans will be verifying the effectiveness of the remediations.
By incorporating Cognisys’ SmartScan into your security measures, you position your organisation to not only respond to but stay ahead of emerging cyber threats. In today’s dynamic cybersecurity landscape, maintaining a step ahead is not only beneficial but imperative. SmartScan emerges as a pivotal component in any modern cyber security strategy.