Top 12 biggest cyber attacks of February 2024
Insights and trends from recent UK cyber threats and breaches from February.

Arjun Pednekar
29th February 2024
The cyber security landscape in the United Kingdom has seen a variety of significant incidents and developments over the past month.
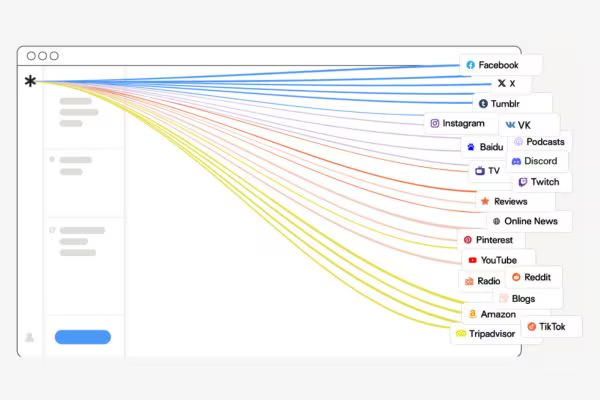
Here are the top 12 biggest cyber attacks and breaches from February that have made an impact on social media:
1. Massive scale cyberattacks
The UK has witnessed a surge in cyberattacks, with nearly a third of businesses reporting breaches or attacks in the past year. Many UK organisations face a challenging cyber security landscape, with a significant portion lacking confidence in their ability to proactively reduce risks. According to recent findings, only 60% of respondents believe their cyber security practices effectively mitigate organisational risks. Cloud infrastructure emerges as a key concern, with over two-thirds of organisations using multi-cloud or hybrid setups citing it as a top risk area. Public cloud infrastructure is deemed particularly risky by 31% of respondents.
The study highlights a concerning trend: despite acknowledging the importance of preventive cyber security measures, many organisations find themselves caught in a reactive cycle. Sixty-five percent of respondents believe dedicating more resources to prevention would enhance their defence against cyberattacks. However, 60% report their security teams are too preoccupied with addressing critical incidents to focus on prevention. This reactive stance is attributed to challenges in obtaining a comprehensive view of the organisation’s attack surface, including identifying unknown assets, cloud resources, code vulnerabilities, and user entitlement systems. The complexity of modern infrastructure exacerbates these difficulties, with multiple cloud systems, identity management tools, and web-facing assets increasing the likelihood of misconfigurations and oversight.
2. Hornetsecurity threat report
Hornetsecurity has highlighted the escalating threat from cybercriminals, which continues to challenge businesses. Phishing remains the most prevalent email attack technique, according to recent findings, increasing by nearly 4% points this year to account for 43.3% of all email attacks. Hornetsecurity CEO Daniel Hofmann emphasises the importance of a robust email security strategy in light of these trends, urging organisations to implement next-gen security services and maintain security awareness across their workplaces to mitigate the risks posed by malicious web links and phishing attacks.
3. Microsoft and HP breaches

4. The ‘Mother of all breaches’
5. LockBit disruption by UK NCA
The UK National Crime Agency (NCA) and international law enforcement, including the FBI, have disrupted LockBit, the world’s most prolific ransomware gang. The NCA has taken control of LockBit’s extortion page and obtained over 1,000 decryption keys for victims. Two LockBit operators were arrested, crypto wallets seized, and international arrest warrants issued. The US DOJ unsealed indictments against Russian nationals. While the takedown is significant given LockBit’s $120 million extortion, its long-term impact remains uncertain.
6. British Library cyberattack
The British Library suffered a significant cyberattack by the Rhysida hacker group, which is believed to be one of the worst cyber incidents in British history. According to Enrico Mariconti, a security expert at UCL, the hacker group Rhysida, believed to be Russian, likely infiltrated the library’s digital systems unnoticed months before. Once they breached the library’s virtual private network (VPN), they could navigate through various online systems, potentially accessing sensitive documents like passport scans and work contracts. Rhysida aimed to sell privileged access to this information for 20 bitcoins (around £600,000). When the library refused to pay the ransom, the hackers published nearly 500,000 files of stolen data on the dark web for free download.
7. Lush cyber security incident
Lush, a UK-based cosmetics retailer, acknowledged a cyber security incident that may have compromised customer or employee data. The extent of the incident’s impact on the company’s production facilities across Europe, Japan, and Australia remains unclear. This incident follows a surge in ransomware attacks across the UK, with 667 organisations compromised in the first half of 2023 alone. Lush is actively investigating the incident with the assistance of external IT forensic specialists. However, the identity of these specialists has not been disclosed. The UK’s National Cyber Security Center (NCSC) offers certified firms under its Cyber Incident Response scheme for organizations affected by such incidents to seek assistance from. Read more about the Lush cyber security incident here.

8. Foxsemicon ransomware attack
Foxsemicon was targeted by a ransomware attack that claimed to have stolen 5 terabytes of data, potentially affecting UK stakeholders. The LockBit ransomware gang, known for its ransomware-as-a-service model, has a history of prolific attacks, including previous victims like Managed Care of North America Inc. and a suspected affiliate arrested in Arizona. The timing of the attack coincides with heightened concerns about cyberattacks in Taiwan, especially with the upcoming general election, prompting calls for support from the U.S. Treasury Department due to increased security vulnerabilities. Read more about the Foxsemicon ransomware attack here.
9. Rhysida ransomware decryption tool
Although not UK-specific, the release of a free decryption tool for Rhysida ransomware by South Korean researchers is a positive development for global cybersecurity efforts. South Korean researchers have unveiled a Rhysida ransomware decryption tool in a preprint paper released on Friday. This tool exploits a vulnerability in Rhysida’s encryption process, enabling files to be recovered through reverse engineering. Developed by Kookmin University and the Korea Internet & Security Agency (KISA), the method predicts encryption keys and the order of file encryption. The automatic decryption tool is freely available on the KISA website. The vulnerability was discovered months earlier by three independent parties and privately circulated to aid Rhysida victims, as noted by ransomware expert Fabian Wosar. Read more about the Rhysida ransomware decryption tool here.
10. OpenAI account takedowns
OpenAI’s takedown of accounts linked to state-backed hackers could have implications for UK users of AI services, as these groups were using AI to further cyber attacks. Microsoft’s recent research reveals nation-state threat actors utilising generative AI, particularly large language models (LLMs) like ChatGPT, in their operations. Although Microsoft reassures enterprises that the increased use of GenAI doesn’t pose an immediate threat, it underscores the need for heightened security measures. The research, conducted by Microsoft Threat Intelligence and OpenAI, identifies five nation-state actors leveraging LLMs for various purposes, including researching technologies, vulnerabilities, regional geopolitics, and high-profile individuals. Currently, AI tools haven’t escalated the danger of attacks, but Microsoft anticipates this could change. This emphasises the importance of ongoing vigilance and adaptation of security protocols to stay ahead of evolving threats posed by nation-state activity utilising AI. Read more about the OpenAI account takedowns here.
11. Facial recognition data breach
The breach of bank accounts using stolen facial recognition data in Asia highlights the growing sophistication of cyberattacks, which could also affect UK financial institutions. Suspected Chinese hackers are conducting a sophisticated campaign targeting Asian bank accounts by using stolen facial recognition data. Dubbed “GoldFactory” by cyber security researchers at Group-IB, this group is extending their activities from a previous Android-based trojan called GoldDigger, which targeted over 50 Vietnamese banks in October 2023. The new campaign involves the use of facial recognition data harvested from victims, indicating a highly unusual approach. Researchers identified four trojans, including GoldPickaxe, which was initially distributed through Apple’s TestFlight platform. When removed, the hackers resorted to social engineering tactics, convincing victims to install a Mobile Device Management (MDM) profile. They posed as government agencies in Thailand, offering a fake “Digital Pension” application, or sent fake utility bill notices with malicious URLs to engage victims. Read more about the Facial recognition data breach here.
12. Insomniac Games ransomware attack
Insomniac Games, a Sony subsidiary known for video games like Marvel’s Spider-Man 2, was hacked by Rhysida ransomware. Over 1.3 million files with personal information were stolen and leaked online. Data breach notification letters were sent to affected individuals. Despite failed negotiations, the studio offered two years of free credit monitoring and identity restoration. This incident highlights the threat of ransomware groups like Rhysida, which have targeted various sectors, including healthcare and military, according to advisories from agencies like CISA and the FBI. Read more about the Insomniac Games ransomware attack here.

These incidents underscore the importance of robust cyber security measures and the need for continuous vigilance by businesses, government entities, and individuals in the UK. The evolving nature of cyber threats demands a proactive and adaptive approach to safeguard sensitive information and critical infrastructure.
If you are concerned about threats to your IT estate, get in touch and one of our cyber experts can discuss how we protect your business.